
Bot Protection on Forms
Keep form endpoints safe from automated abuse with layered defenses—rate limits, CAPTCHAs, and targeted verification tha
Stay updated with trends, tips, and insights in digital innovation.

Keep form endpoints safe from automated abuse with layered defenses—rate limits, CAPTCHAs, and targeted verification tha
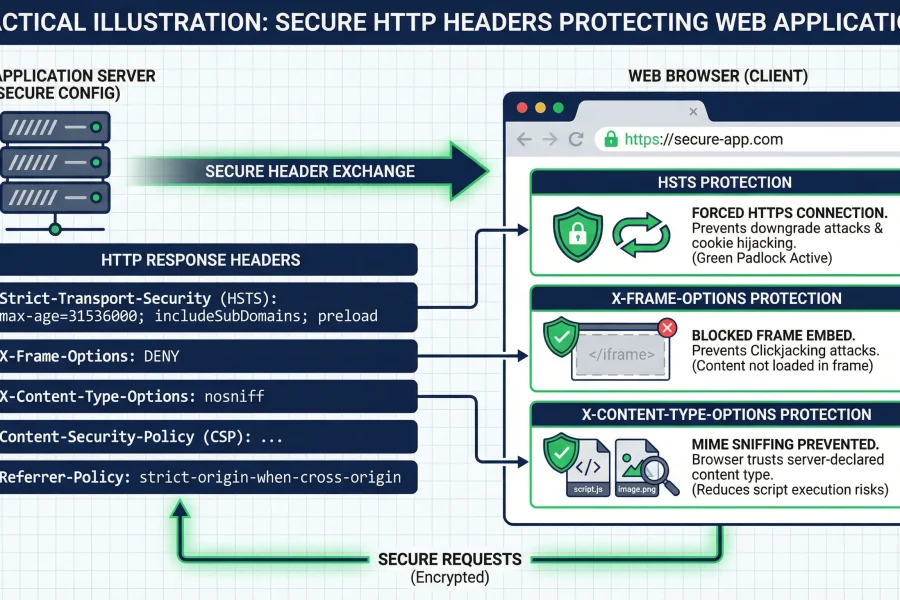
Deploy and tune essential HTTP security headers, validate their impact in staging, and keep watch on blocked responses a

Set CSP response headers, refine policy rules by asset and origin, and validate across Chrome, Firefox, and Safari to st
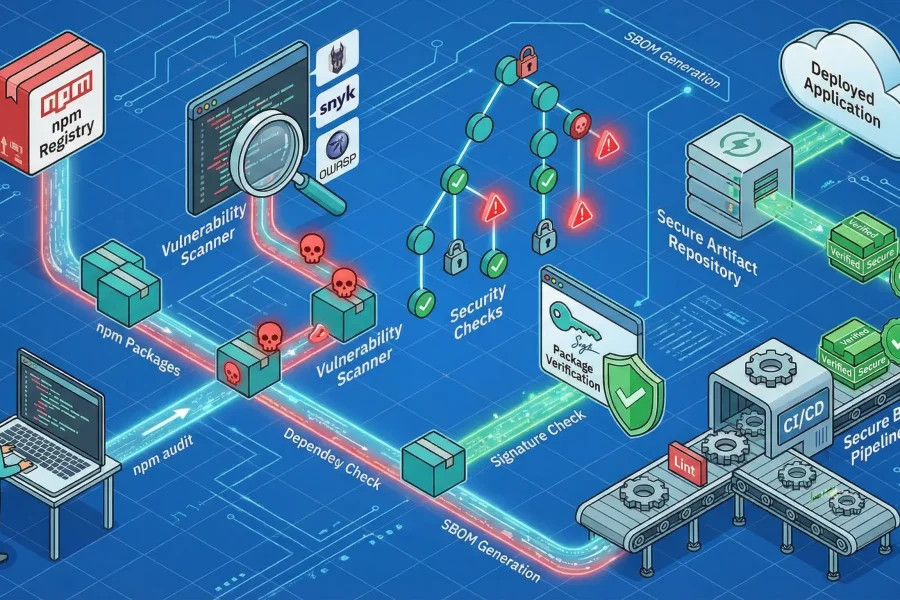
Scan your frontend package supply chain — spot vulnerable dependencies, pin or lock risky versions, and stop unsafe pack
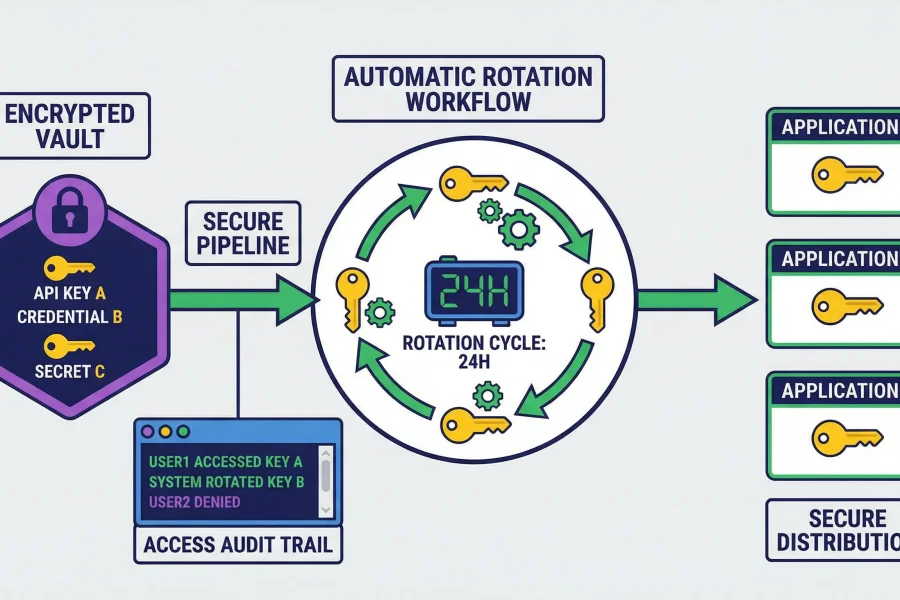
Put secrets in a hardened vault, issue short‑lived credentials, and automate rotations to shrink exposure and keep CI/CD
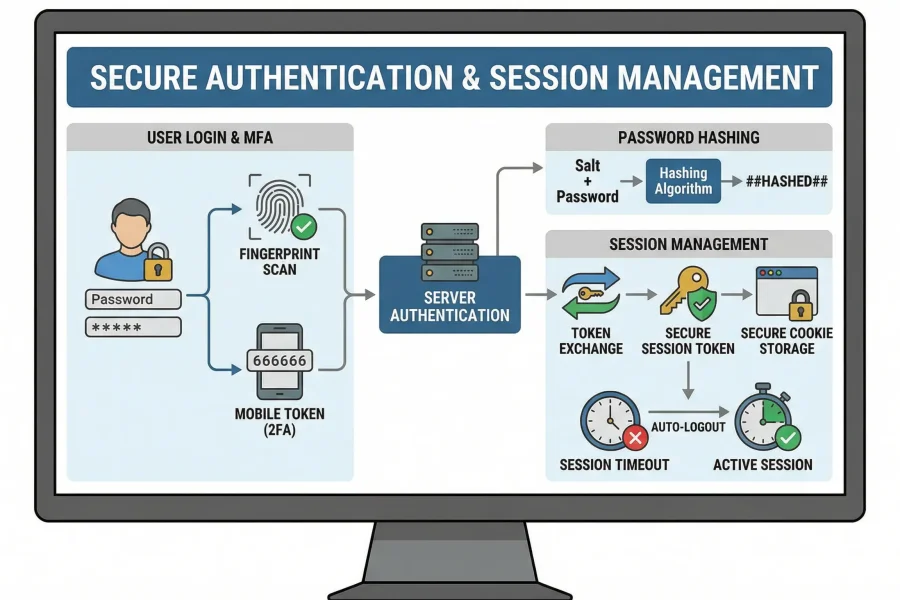
Lock down authentication flows and tighten session controls: set sensible token lifetimes, define logout semantics, and

Lock down APIs with strong authentication, fine-grained authorization, strict payload validation, and sensible rate limi
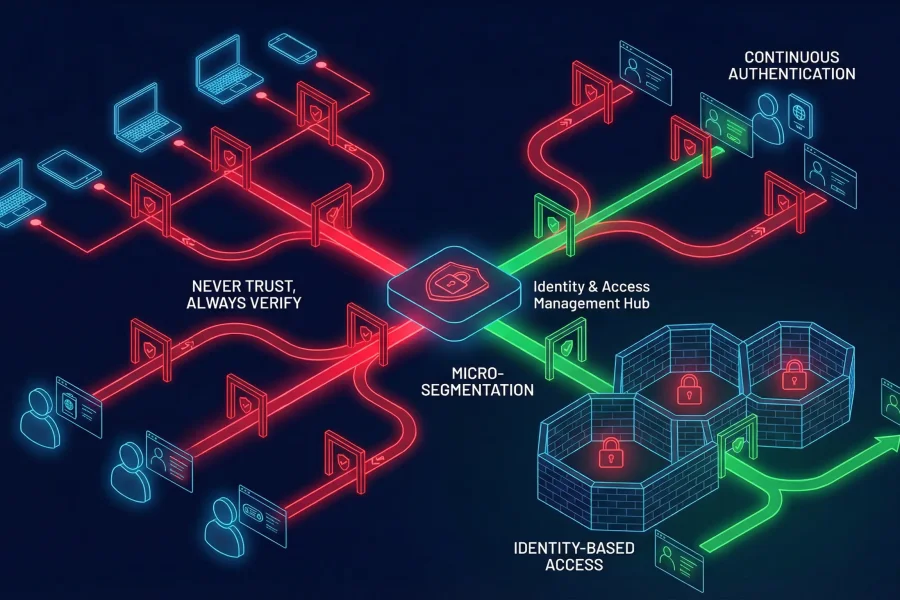
Apply Zero Trust fundamentals: map and audit trust boundaries across your network, enforce least privilege everywhere, a

Convert OWASP Top 10 findings into prioritized remediation tickets so teams can deliver fast, verifiable fixes that cut
We build websites, mobile apps, and e-commerce platforms, and deliver SEO, PPC, and content marketing for businesses across the UK.