←
Back to Blog
Cybersecurity
•
•
Team PixelPilot
•
5 min read
API Security Best Practices
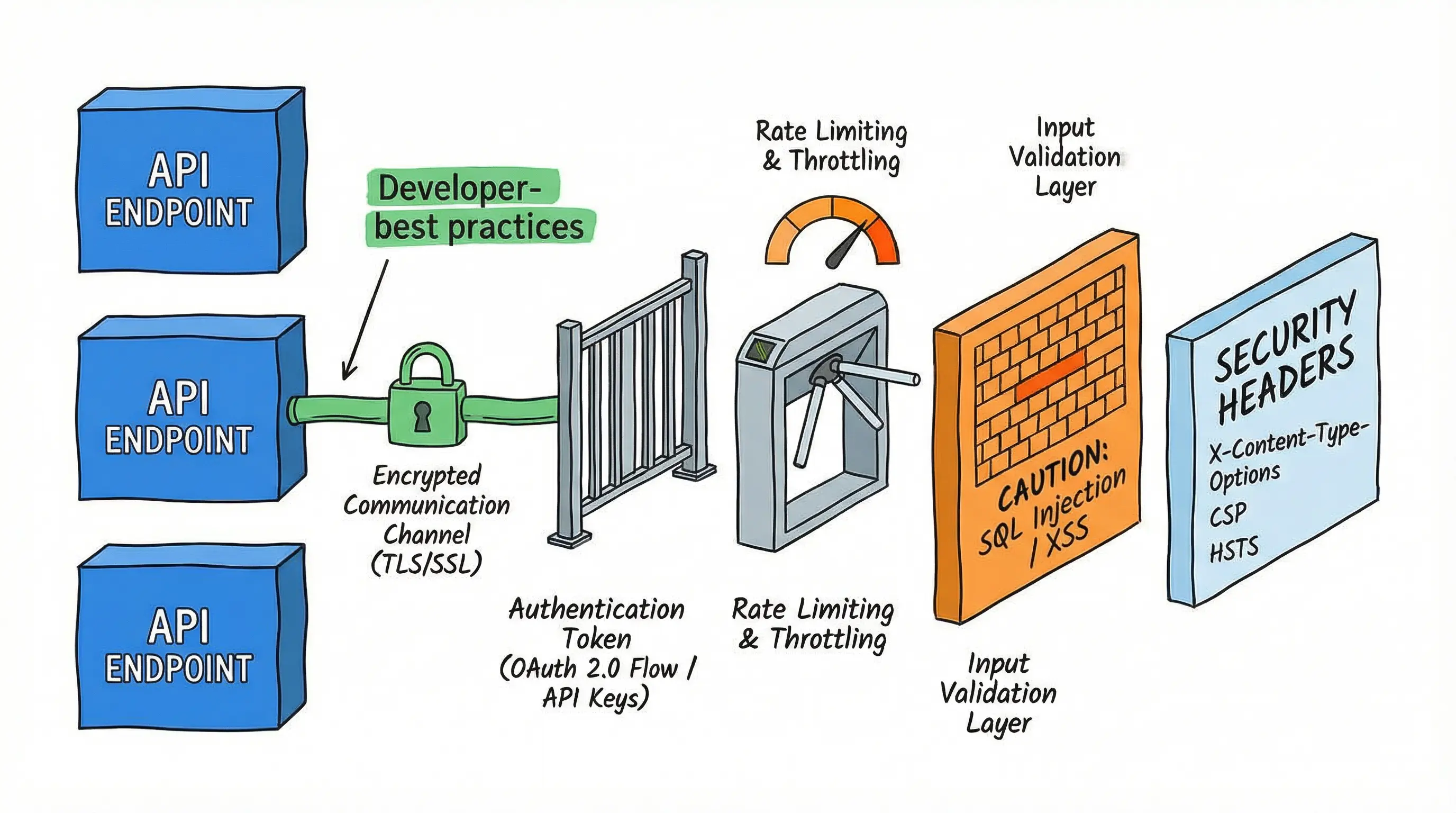
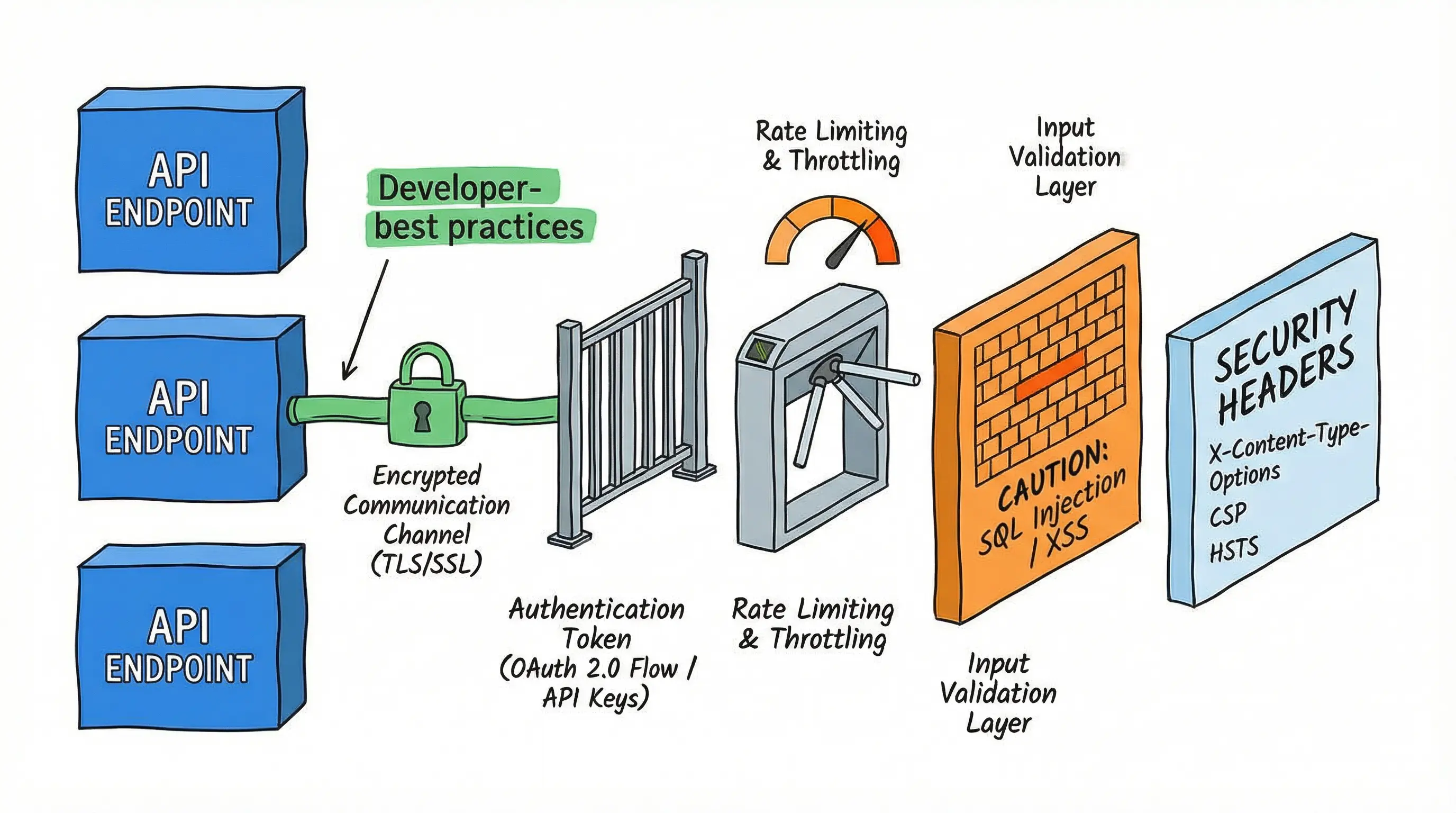
Lock down APIs with strong authentication, fine-grained authorization, strict payload validation, and sensible rate limi
Introduction
APIs (Application Programming Interfaces) are the backbone of modern software development, enabling applications to communicate, exchange data, and integrate services. With the rise of microservices, cloud computing, and third-party integrations, APIs have become a primary target for cyberattacks.
Securing APIs is essential to protect sensitive data, maintain service availability, and ensure compliance with regulatory frameworks. Poorly secured APIs can result in data breaches, unauthorized access, and reputational damage, making API security a strategic priority.
This article provides a comprehensive guide to API security best practices, covering design principles, authentication, encryption, monitoring, and governance.
Understanding API Security
API security ensures that only authorized clients and users can access data and functionality, while protecting the system from malicious or unintended requests. It involves:
Authentication – Verifying the identity of the client or user
Authorization – Ensuring users only perform permitted actions
Data Integrity – Preventing tampering during transmission
Confidentiality – Protecting sensitive information
Availability – Safeguarding against denial-of-service attacks
Common API security threats include:
Broken Authentication and Authorization – Allowing unauthorized access
Excessive Data Exposure – Returning sensitive data unnecessarily
Injection Attacks – Exploiting query or command inputs
Rate Limiting Bypass – Flooding the API to disrupt service
Man-in-the-Middle Attacks – Intercepting unencrypted traffic
Insufficient Logging and Monitoring – Failing to detect attacks promptly
Design Principles for Secure APIs
1. Principle of Least Privilege
Grant the minimum permissions necessary to users and clients
Avoid exposing internal endpoints or sensitive fields unnecessarily
2. Defense in Depth
Use multiple layers of protection rather than relying on a single security mechanism
Combine authentication, input validation, encryption, rate limiting, and monitoring
3. Secure by Default
Design APIs to be secure out-of-the-box
Require authentication for all endpoints unless explicitly public
4. Fail Securely
APIs should return safe error messages that do not expose internal system details
Avoid detailed stack traces or sensitive configuration in responses
Authentication and Authorization
Authentication
OAuth 2.0 – Industry standard for delegated access
Allows third-party apps to access resources without sharing passwords
Supports token expiration, refresh tokens, and scopes
JWT (JSON Web Tokens) – Encodes user identity and claims
Ensure signing and verification using secure keys
Use short-lived tokens for session security
API Keys – Simple but less secure; best combined with other methods
Rotate keys regularly and enforce limits
Mutual TLS (mTLS) – Certificates verify both client and server
Ensures encrypted, trusted communication for sensitive APIs
Authorization
Role-Based Access Control (RBAC) – Grants access based on user roles
Attribute-Based Access Control (ABAC) – Uses contextual information (time, location, device) for fine-grained permissions
Validate authorization on every request, not just during login
Input Validation and Data Protection
Validate All Inputs – Protect against injection attacks (SQL, NoSQL, XML, JSON)
Sanitize Outputs – Ensure data returned to clients does not expose sensitive fields
Use Parameterized Queries – Avoid concatenated strings in database calls
Implement Strong Encryption
Use TLS 1.2 or higher for transport security
Encrypt sensitive data at rest using AES-256 or equivalent
Mask Sensitive Data – Avoid returning full personal or financial information unless strictly necessary
Rate Limiting and Throttling
Prevent abuse by limiting requests per user, IP, or API key
Protects against DDoS attacks and system overloads
Strategies:
Fixed Window – Limit requests in a fixed interval
Sliding Window – Smooths traffic spikes
Token Bucket – Allows bursts while enforcing overall limits
Logging, Monitoring, and Incident Response
Log all API activity securely, including authentication attempts, errors, and high-volume requests
Monitor anomalies in traffic patterns or failed requests
Use automated alerts for suspicious activity
Maintain an incident response plan to isolate compromised APIs quickly
Versioning and Deprecation
Ensure security mechanisms remain effective across API versions
Deprecate older versions safely to avoid exposing vulnerabilities
Document breaking changes and require clients to upgrade securely
Testing and Validation
Penetration Testing – Simulate attacks to identify vulnerabilities
Security Scanning – Automated scanning for common flaws (OWASP API Security Top 10)
Fuzz Testing – Send malformed inputs to detect crashes or unexpected behavior
Continuous Integration Security Checks – Integrate tests into CI/CD pipelines
API Gateway and Security Middleware
Use API gateways to centralize security controls
Features:
Authentication and authorization enforcement
Rate limiting and throttling
Request validation and logging
IP filtering and geofencing
Provides consistent security across multiple services and endpoints
Real-World Considerations
Third-Party Integrations – Vet partners for secure practices and restrict access scopes
Microservices Architecture – Ensure secure communication between services via mTLS or service mesh
Cloud APIs – Follow cloud provider best practices for keys, IAM roles, and audit logging
Performance vs. Security – Optimize token validation, encryption, and logging for low-latency APIs
Compliance and Regulatory Requirements
GDPR / CCPA – Protect personal data and respect privacy rights
PCI-DSS – Secure payment-related APIs
HIPAA – Protect health data in healthcare applications
Ensure audit logs and access controls meet regulatory standards
Best Practices Checklist
Authenticate and authorize every request
Validate all inputs and sanitize outputs
Encrypt data in transit and at rest
Implement rate limiting and throttling
Monitor API traffic and log suspicious activity
Apply defense in depth and least privilege principles
Version APIs securely and deprecate old versions
Test continuously with security scans and penetration testing
Educate developers on API security risks and secure coding practices
Business Benefits
Reduced risk of data breaches and financial losses
Maintained customer trust and reputation
Compliance with industry regulations and audits
Improved reliability and availability of API-based services
Scalable, secure integrations with partners, third-party services, and microservices
Challenges and Considerations
Balancing security with usability for developers and clients
Keeping security measures updated against evolving threats
Managing keys, tokens, and credentials securely
Securing high-volume APIs without affecting performance
Coordinating security across microservices and third-party integrations
Conclusion
API security is a critical component of modern digital architecture. By implementing authentication, authorization, input validation, encryption, rate limiting, and monitoring, organizations can protect their APIs from malicious actors while enabling seamless integrations.
A layered, proactive approach, combined with continuous testing, logging, and governance, ensures APIs remain reliable, compliant, and resilient in an increasingly connected digital ecosystem.
Securing APIs is not a one-time task—it is an ongoing strategic effort that safeguards data, protects users, and ensures business continuity.
Need help with your digital project?
Our team builds websites, mobile apps, e-commerce platforms and runs data-driven marketing campaigns for businesses across the UK.