←
Back to Blog
Cybersecurity
•
•
Team PixelPilot
•
4 min read
Zero Trust Fundamentals
Apply Zero Trust fundamentals: map and audit trust boundaries across your network, enforce least privilege everywhere, a
Introduction
As organizations rely more on digital systems, data, and online services, protecting information has become a critical priority. Traditional security methods were built on the idea that everything inside a company’s network could be trusted. However, modern threats have shown that this approach is no longer effective. Zero Trust is a modern security model that changes how organizations think about protection by assuming that no user or system should be trusted automatically.
What Is Zero Trust?
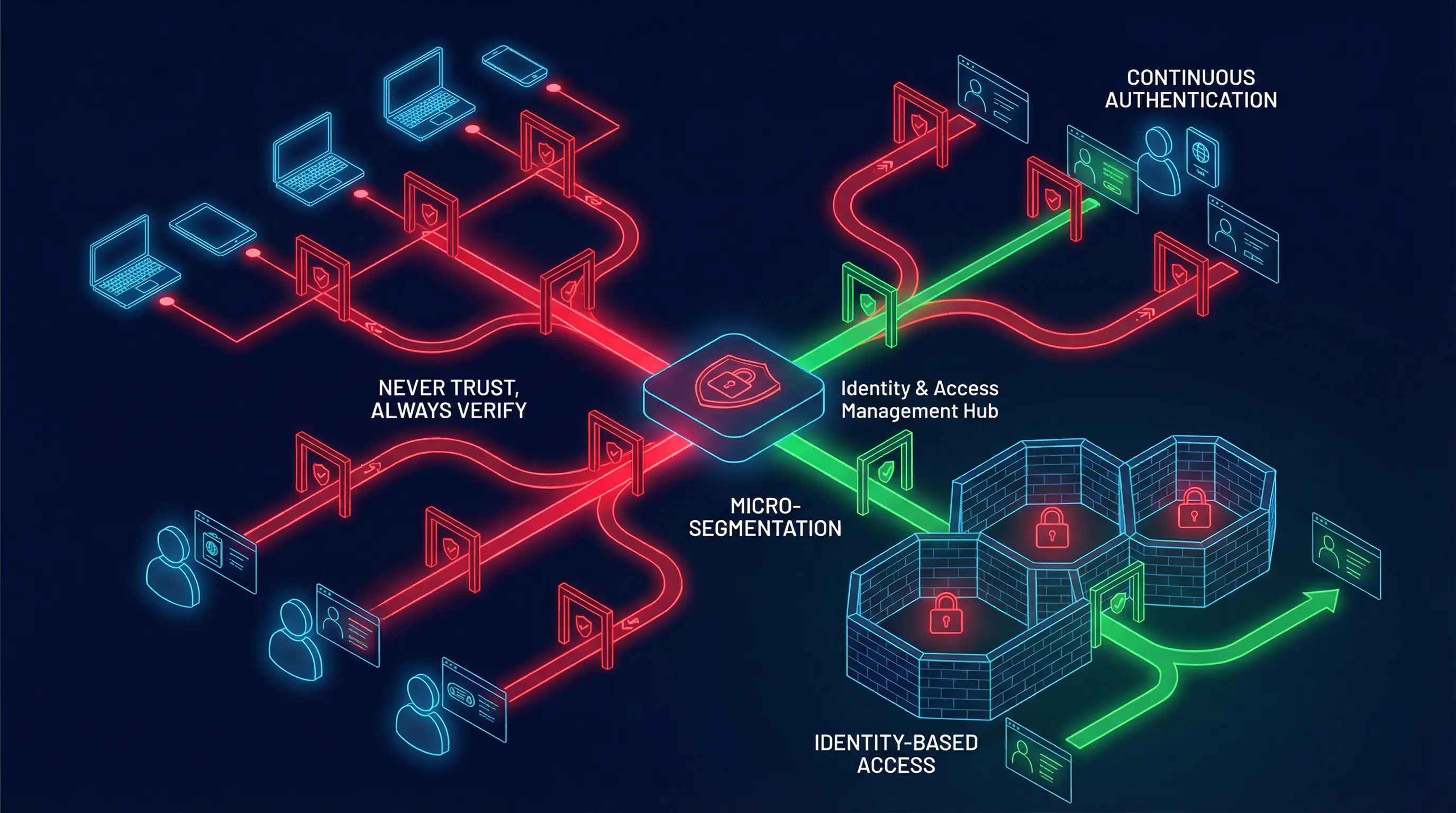
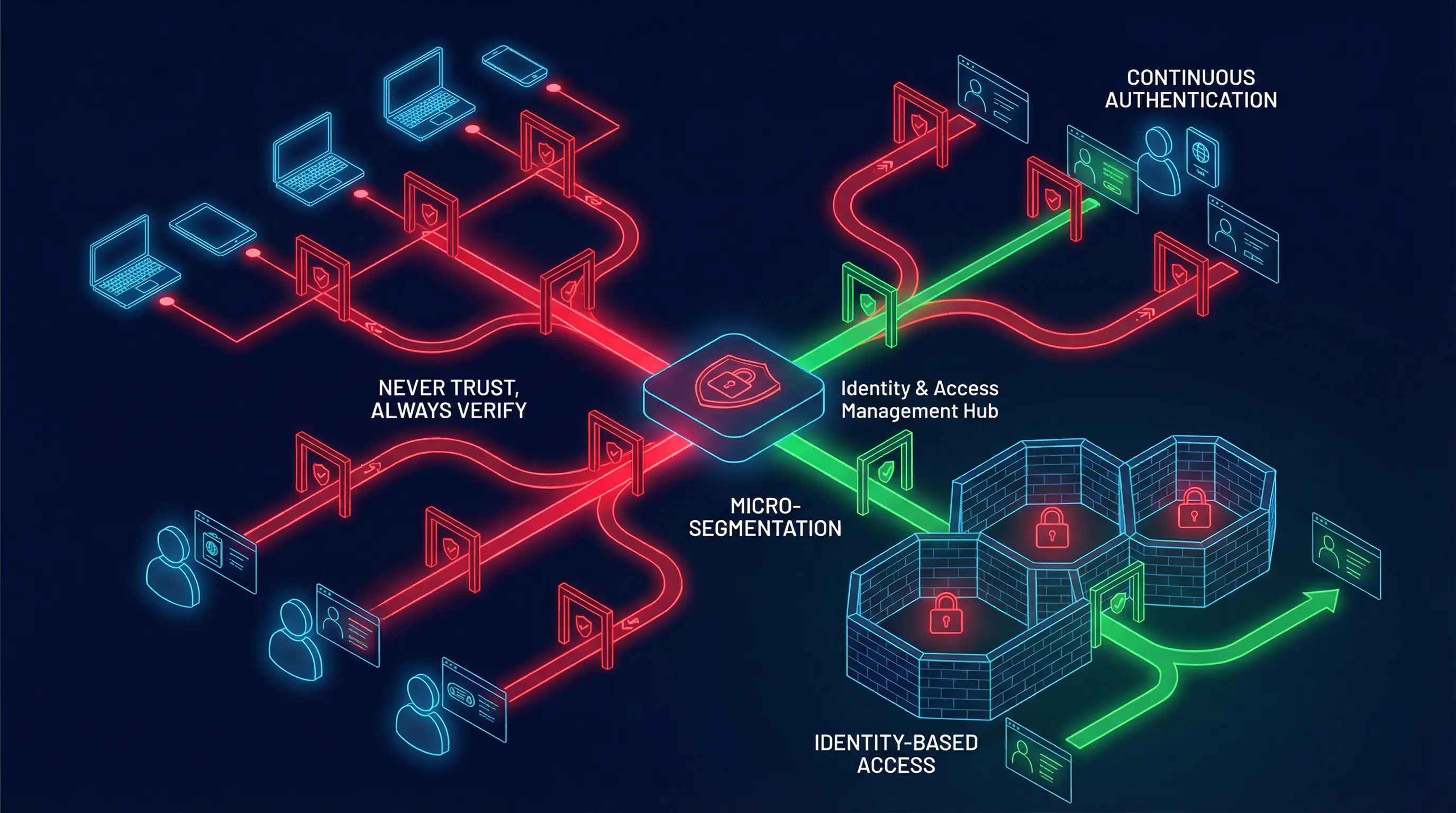
Zero Trust is a security approach based on a simple principle: never trust, always verify. This means that every user, device, and system must prove it is safe before gaining access, regardless of whether it is inside or outside the organization’s network.
Instead of relying on a single security barrier, Zero Trust continuously checks identity, permissions, and behavior. Access is granted only when it is truly needed and only for the specific task being performed.
Why Traditional Security Is No Longer Enough
In the past, security focused on building strong defenses around a network, similar to locking the doors of a building. Once someone was inside, they could often move freely. This approach worked when systems were simple and located in one place.
Today, employees work remotely, use personal devices, and access cloud services from anywhere. Cyber threats are also more advanced and often come from inside the network. Zero Trust addresses these challenges by removing the idea of a trusted internal environment.
Core Principles of Zero Trust
Zero Trust is built on several key principles. First, verify identity at all times. Every access request must be checked, even if the user has logged in before. Second, limit access to what is necessary. Users receive only the permissions they need to do their job, nothing more.
Another principle is continuous monitoring. Systems watch for unusual activity and can adjust access in real time. This helps detect and stop threats before they cause damage.
Protecting Users and Devices
In a Zero Trust model, security focuses on both users and devices. A user must confirm their identity, often through multiple steps such as passwords and verification codes. Devices are also checked to ensure they meet security standards before being allowed access.
If a device is outdated or compromised, access can be restricted or denied. This helps prevent attackers from using weak or stolen devices to enter systems.
Data Protection and Access Control
Zero Trust places strong emphasis on protecting data itself. Sensitive information is secured with strict access rules and encryption. Even if attackers gain access to part of the system, they cannot easily reach critical data.
Access decisions are made based on context, such as who is requesting access, from where, and for what purpose. This reduces the risk of data leaks and misuse.
Business Benefits of Zero Trust
Beyond security, Zero Trust offers clear business advantages. It reduces the impact of cyber attacks by limiting how far attackers can move. It also supports flexible work environments, allowing employees to work safely from anywhere.
By improving visibility and control, organizations can meet regulatory requirements more easily and build trust with customers and partners.
Challenges and Implementation
Adopting Zero Trust is not an overnight process. It requires planning, updated tools, and changes in how teams think about security. However, organizations can start small by protecting critical systems first and expanding gradually.
Education and clear communication are essential to ensure employees understand why these changes are necessary and how they improve overall security.
Conclusion
Zero Trust represents a shift from traditional security thinking to a more realistic and resilient approach. By assuming that threats can come from anywhere and verifying every access request, organizations can better protect their systems, data, and users.
In a world of growing digital risk, Zero Trust is not just a security trend—it is a foundational strategy for long-term protection and trust.
Need help with your digital project?
Our team builds websites, mobile apps, e-commerce platforms and runs data-driven marketing campaigns for businesses across the UK.