←
Back to Blog
Cybersecurity
•
•
Team PixelPilot
•
3 min read
Secrets Management and Rotation
Put secrets in a hardened vault, issue short‑lived credentials, and automate rotations to shrink exposure and keep CI/CD
Introduction
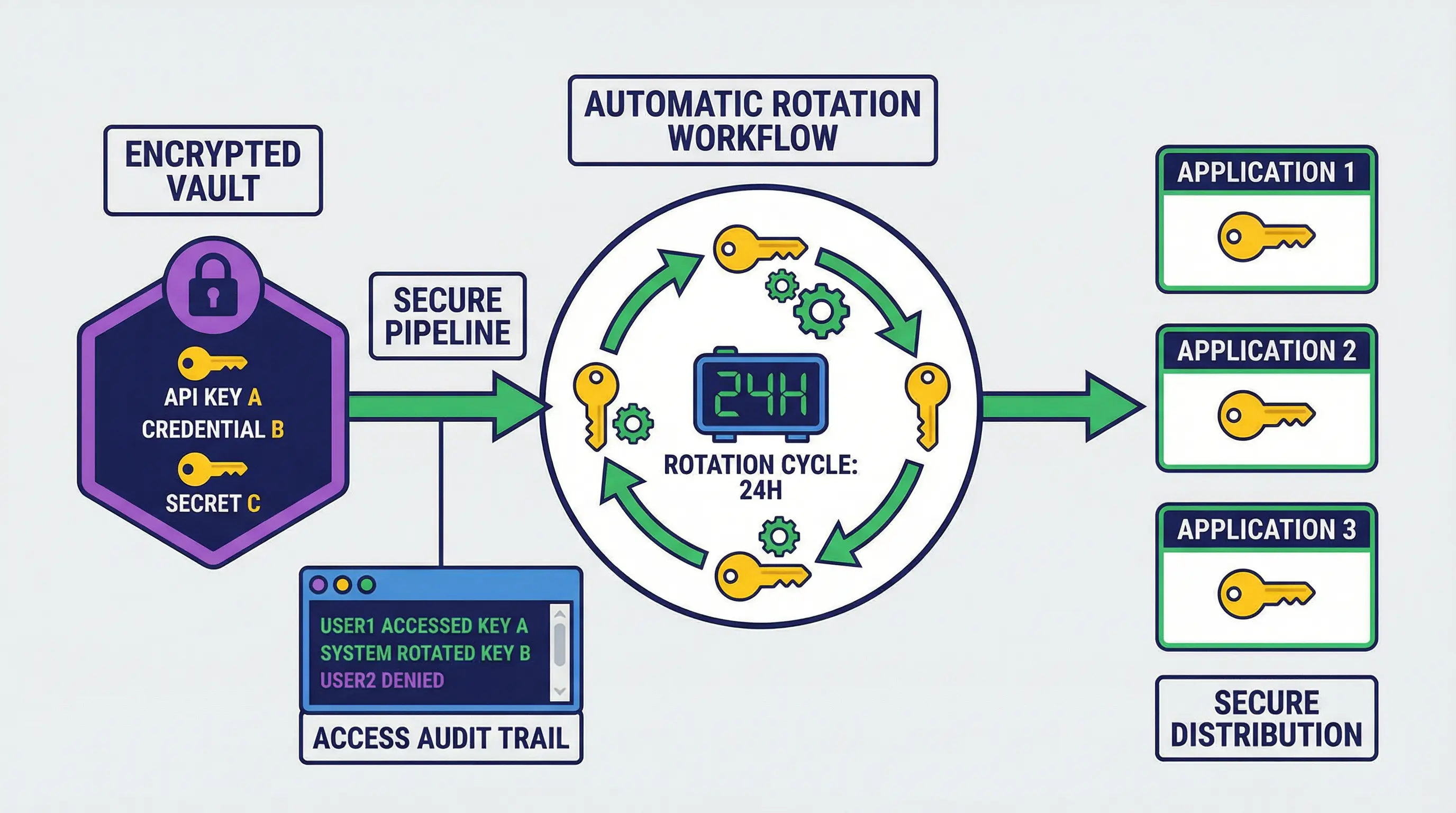
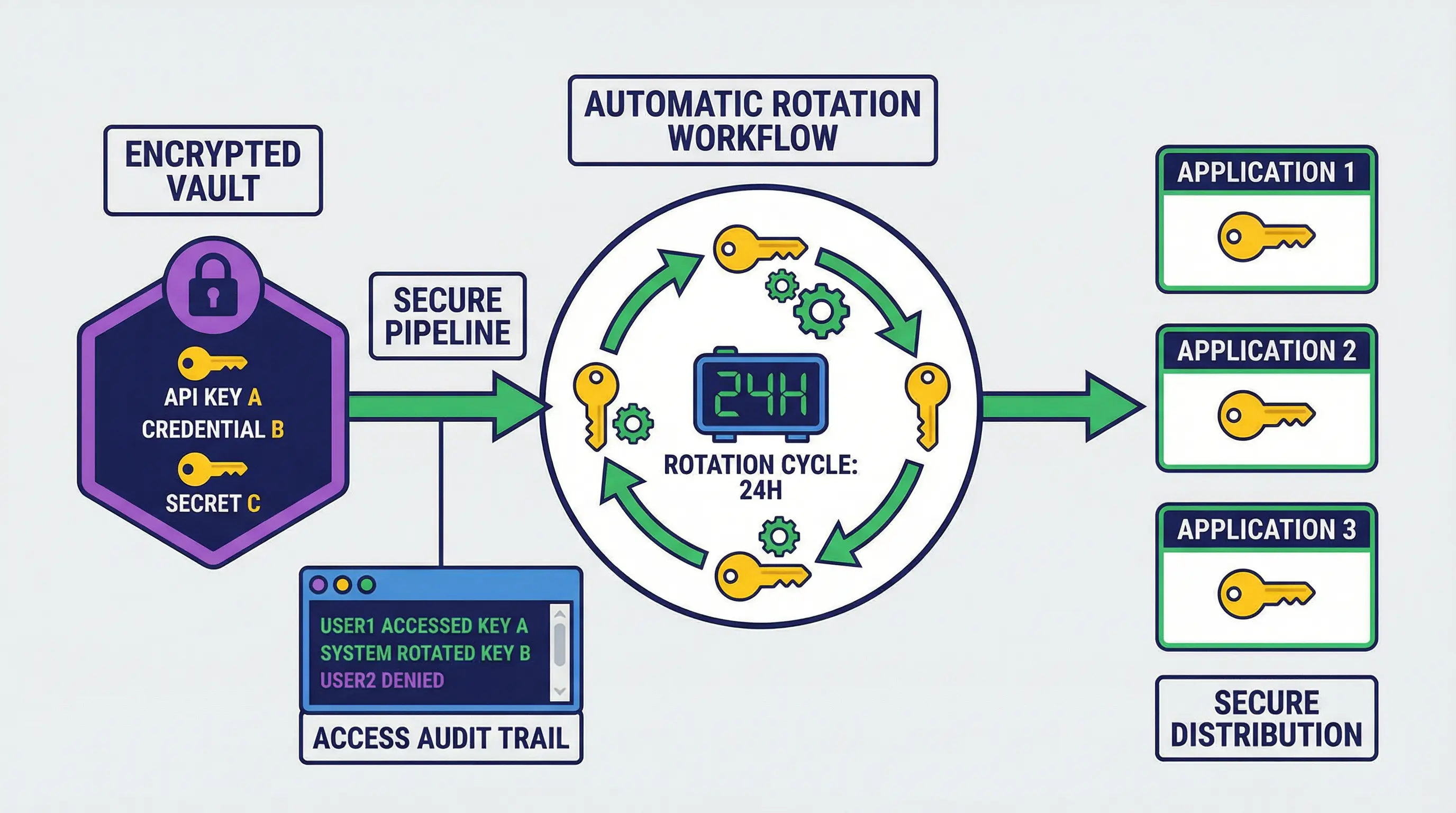
Modern applications, cloud services, and infrastructure rely on sensitive information such as passwords, API keys, certificates, and tokens. Collectively, these are called secrets. Proper management of secrets is critical to prevent unauthorized access, data breaches, and operational disruptions. Secrets management and rotation provide a structured approach to storing, using, and updating these sensitive credentials securely.
What Is Secrets Management
Secrets management is the process of securely storing, accessing, and using sensitive information required by applications and systems. Instead of hardcoding secrets into code or configuration files, organizations use centralized systems to control access, monitor usage, and enforce security policies.
Benefits of Centralized Secrets Management
Reduces the risk of accidental exposure in code repositories or logs
Provides a single point for auditing and monitoring access
Enables secure sharing across teams and environments
Integrates with applications and infrastructure for automated access
The Importance of Secrets Rotation
Secrets rotation is the practice of regularly updating passwords, API keys, and other credentials. Even if a secret is compromised, rotation limits the window of opportunity for attackers. Automated rotation ensures that credentials are changed on schedule without disrupting applications or services.
Key Principles of Secrets Rotation
Rotate secrets frequently based on risk and sensitivity
Use automation to minimize human error and downtime
Immediately revoke secrets when a compromise is suspected
Maintain backward compatibility during rotation to avoid service interruptions
Best Practices for Secrets Management
Use a Dedicated Secrets Management System
Tools like HashiCorp Vault, AWS Secrets Manager, and Azure Key Vault provide secure storage, controlled access, and auditing capabilities. They also integrate with applications and cloud services to retrieve secrets dynamically.
Avoid Hardcoding Secrets
Storing secrets directly in code, configuration files, or version control increases the risk of accidental leaks. Use environment variables or secure connectors provided by secret management tools.
Implement Role-Based Access Control
Access to secrets should follow the principle of least privilege. Only systems or users that need a secret for their tasks should be granted access. This reduces exposure and prevents unnecessary risk.
Monitor and Audit Access
Logging every access to secrets provides visibility and accountability. Regular audits help detect anomalies, misuse, or unauthorized attempts to access sensitive information.
Benefits for Organizations
Effective secrets management and rotation improve security, reduce the risk of breaches, and support compliance with regulations. Automated rotation reduces operational overhead while maintaining secure access. Organizations can maintain confidence that their sensitive credentials are protected and used responsibly.
Challenges and Considerations
Implementing secrets management requires planning and integration. Challenges include:
Ensuring seamless integration with existing applications and infrastructure
Balancing security with operational efficiency
Coordinating secret rotation without service downtime
Training teams to follow proper access and usage procedures
Despite these challenges, the long-term benefits of reduced risk and improved operational security outweigh the initial effort.
Conclusion
Secrets management and rotation are essential practices for modern organizations that rely on digital systems and cloud services. By securely storing secrets, controlling access, and rotating credentials regularly, organizations can protect sensitive information, prevent breaches, and maintain operational continuity.
In a world of increasing cyber threats and regulatory requirements, secrets management and rotation are foundational elements of a robust security strategy.
Need help with your digital project?
Our team builds websites, mobile apps, e-commerce platforms and runs data-driven marketing campaigns for businesses across the UK.