←
Back to Blog
Cybersecurity
•
•
Team PixelPilot
•
5 min read
OWASP Top 10: Practical Fixes
Convert OWASP Top 10 findings into prioritized remediation tickets so teams can deliver fast, verifiable fixes that cut
Introduction
Web application security is a critical concern for every organization. Attacks targeting common vulnerabilities can lead to data breaches, financial loss, and reputational damage. The Open Web Application Security Project, or OWASP, publishes the Top 10 most critical web application vulnerabilities. Understanding these risks and implementing practical fixes helps developers and teams secure applications effectively.
The OWASP Top 10 is updated periodically to reflect evolving threats and trends. This guide provides actionable steps to mitigate each vulnerability while maintaining usability and performance.
1. Broken Access Control
The Risk
Broken access control occurs when users can perform actions beyond their permissions. This can lead to unauthorized data access, privilege escalation, or manipulation of system resources.
Practical Fixes
Implement role-based or attribute-based access control
Deny access by default and explicitly allow only necessary actions
Verify permissions on the server side for every request
Avoid exposing sensitive endpoints in client-side code
Regularly audit and test access control rules
2. Cryptographic Failures
The Risk
Weak encryption, improper key management, or storing sensitive data in plain text exposes users to attacks such as credential theft or data leaks.
Practical Fixes
Use strong, modern encryption algorithms (AES-256, RSA-2048)
Store passwords using secure hashing with salts (bcrypt, Argon2)
Encrypt sensitive data in transit using HTTPS/TLS
Manage encryption keys securely and rotate them regularly
Avoid custom cryptography or outdated algorithms
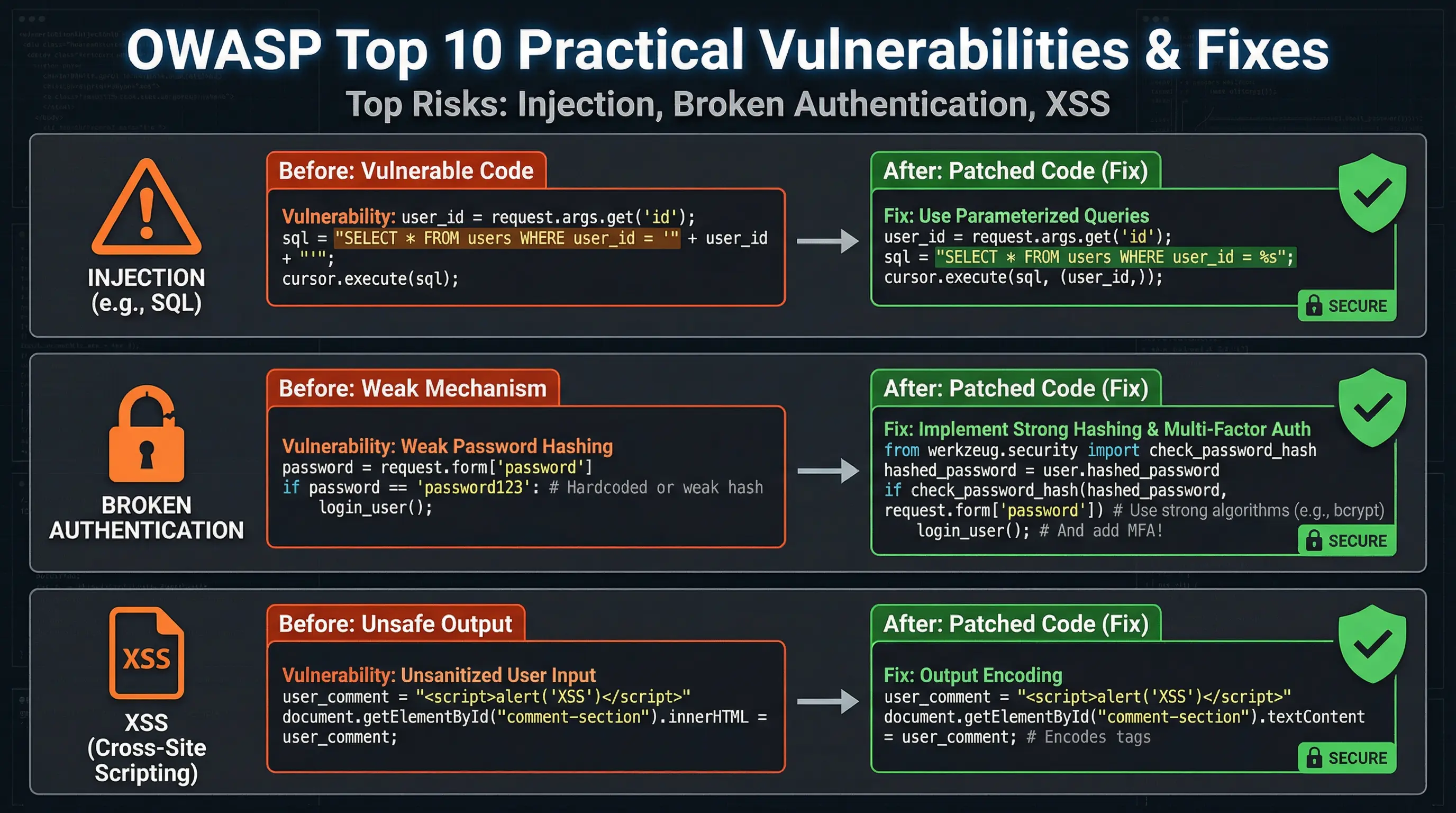
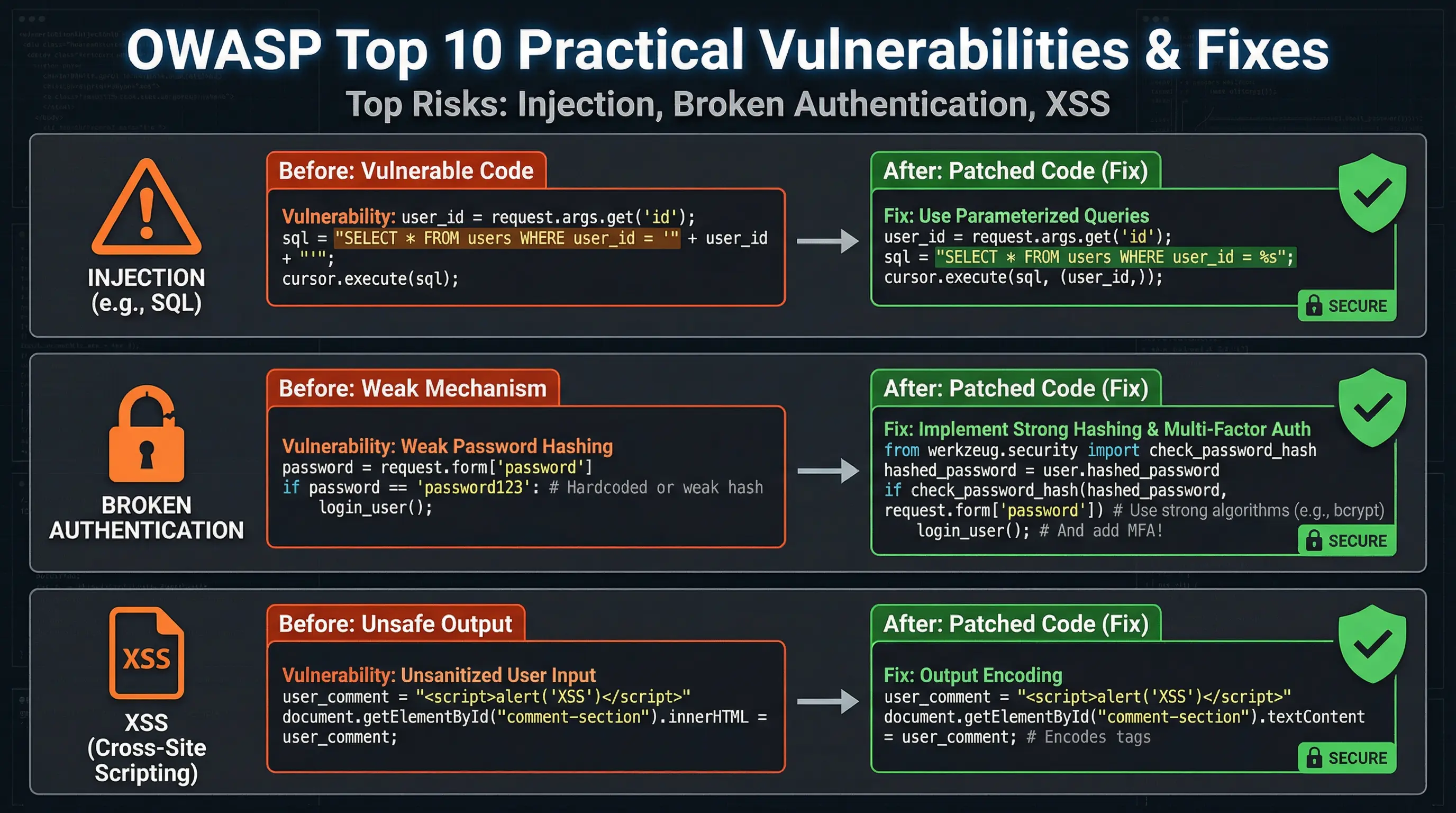
3. Injection
The Risk
Injection attacks occur when untrusted input is executed as code or a command, such as SQL, NoSQL, or command injections. These can compromise databases, servers, or other systems.
Practical Fixes
Use parameterized queries or prepared statements
Validate and sanitize all user input
Avoid constructing queries or commands dynamically
Apply least privilege for database accounts
Employ web application firewalls to filter malicious payloads
4. Insecure Design
The Risk
Insecure design refers to fundamental flaws in architecture or logic that introduce vulnerabilities. Unlike implementation bugs, these are inherent in how the application is built.
Practical Fixes
Adopt security by design principles
Conduct threat modeling during development
Use secure frameworks and libraries
Incorporate security reviews into design phases
Implement proper error handling and logging without exposing sensitive information
5. Security Misconfiguration
The Risk
Security misconfiguration arises from default settings, unnecessary features, or improper permissions. It is one of the most common vulnerabilities and affects both servers and applications.
Practical Fixes
Remove default accounts and change default passwords
Disable unnecessary services, features, or endpoints
Apply security patches promptly for servers, libraries, and frameworks
Set proper HTTP headers for security, such as Content Security Policy, X-Frame-Options, and HSTS
Regularly audit configurations and access rights
6. Vulnerable and Outdated Components
The Risk
Using outdated software, libraries, or frameworks can introduce known vulnerabilities that attackers exploit.
Practical Fixes
Maintain an up-to-date inventory of all components and dependencies
Subscribe to security alerts for frameworks and libraries
Update and patch dependencies regularly
Remove unused components to reduce attack surface
Use automated tools like Dependabot, Snyk, or OWASP Dependency-Check to monitor vulnerabilities
7. Identification and Authentication Failures
The Risk
Weak authentication allows attackers to impersonate users or gain access to sensitive data. Common failures include poor password policies, exposed session IDs, or lack of multi-factor authentication.
Practical Fixes
Enforce strong password policies and complexity requirements
Implement multi-factor authentication (MFA) for sensitive actions
Secure session management using HTTP-only and secure cookies
Limit login attempts and implement account lockout policies
Monitor authentication events for anomalies
8. Software and Data Integrity Failures
The Risk
Data integrity failures occur when software or data is modified maliciously or unintentionally. This includes tampering with updates, logs, or transmitted data.
Practical Fixes
Sign software updates and validate integrity before installation
Use checksums or hashes to verify data consistency
Encrypt data at rest and in transit
Protect logs from tampering by restricting access and monitoring changes
Implement automated integrity checks in critical workflows
9. Security Logging and Monitoring Failures
The Risk
Without proper logging and monitoring, attacks can go unnoticed, and incident response becomes slow and ineffective.
Practical Fixes
Implement centralized logging for all critical actions and security events
Monitor logs continuously for suspicious activity
Set up alerting for anomalies, failed logins, and data access violations
Retain logs for a sufficient period to support forensic analysis
Regularly test detection and response procedures
10. Server-Side Request Forgery
The Risk
Server-side request forgery occurs when an attacker tricks a server into making unintended requests, often leading to internal resource access or data exfiltration.
Practical Fixes
Validate and sanitize all user-supplied URLs or input
Restrict server requests to trusted destinations
Use network-level controls such as firewalls and whitelisting
Implement timeout and rate-limiting for server requests
Avoid exposing internal services directly to user input
Integrating OWASP Fixes into Development
Securing applications requires integrating these fixes into the software development lifecycle:
Secure coding practices: Train developers on secure design and implementation
Code reviews and static analysis: Detect vulnerabilities before deployment
Dynamic testing and penetration testing: Identify issues in runtime environments
Continuous monitoring: Ensure security remains effective as the application evolves
Business Benefits
Implementing practical OWASP fixes:
Reduces the risk of costly data breaches
Enhances user trust and brand reputation
Ensures compliance with regulations like GDPR, HIPAA, and PCI DSS
Improves application reliability and reduces downtime from attacks
Conclusion
The OWASP Top 10 highlights the most critical web application vulnerabilities. Addressing them with practical fixes is essential for building secure, trustworthy applications. By applying best practices for access control, input validation, configuration, authentication, and monitoring, organizations can significantly reduce risk, protect sensitive data, and maintain user trust.
Security is not a one-time task but a continuous process. Integrating OWASP principles into development, deployment, and monitoring ensures that applications remain secure as threats evolve.
Need help with your digital project?
Our team builds websites, mobile apps, e-commerce platforms and runs data-driven marketing campaigns for businesses across the UK.